When two separate Okta tenants need to share application access — partner organizations, M&A scenarios, separate business units — Org2Org is the native solution. It federates the two orgs via SAML 2.0 and uses the Okta provisioning API to sync users automatically. This walkthrough uses Dropbox Business as the target application, but the Org2Org setup itself is the same regardless of what app you’re connecting.
- Two Okta organizations — the Identity Provider (IdP) org must be a paid or partner account; the Service Provider can be developer/paid/partner
- Super Admin access on both tenants
- Target application supporting SAML 2.0 (Dropbox Business used here)
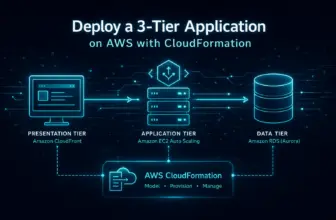
Architecture
Identity Provider (Org1)
Owns the user identities. Authenticates users and issues SAML assertions to Org2.
Service Provider (Org2)
Hosts the applications. Receives federated users from Org1 and provisions them via the API.
Provisioning link
Org1 uses an API token from Org2 to create and sync users automatically on first login (JIT).
Step 1 — Configure the Target Application (SP Side)
Start in the Service Provider tenant. Add the application and configure it before touching the Org2Org federation — you’ll need values from the app to complete the SP side later.
- Applications → Browse App Catalog → search for Dropbox Business → Add Integration
- Sign-On tab → copy the Sign-on URL and download the Signing Certificate
- In Dropbox Admin Console → Settings → Security → Single sign-on: upload the cert and paste the Sign-on URL
Provisioning settings
# Advanced Sign-On Settings
Silent Provisioning: Enabled
Username: Okta username
# Provisioning > To App
✓ Create Users
✓ Update User Attributes
✓ Deactivate UsersStep 2 — Install the Org2Org App (IdP Side)
- In the Identity Provider tenant: Applications → Browse App Catalog → search Okta Org2Org → Add
- In the configuration wizard, set the Base URL to the Service Provider tenant URL (e.g.
https://dev-12345.okta.com) - After installation: Sign-On tab → More Details → copy the Issuer URI, Sign-on URL, and download the Signature Certificate
Step 3 — Create the SAML IdP (SP Side)
- In the Service Provider tenant: Security → Identity Providers → Add Identity Provider → SAML 2.0
General settings
Name: Org1 IdP
IdP Username: idpuser.subjectNameId
Match Against: Okta UsernameSAML endpoints
IdP Issuer URI: [Issuer URI from Org1]
IdP SSO URL: [Sign-on URL from Org1]
Certificate: [upload cert from Org1]
Account Link Policy: Automatic
Provisioning: Create user if neededStep 4 — Configure Cross-Tenant Provisioning
Generate an API token (SP side)
- In the Service Provider tenant: Security → API → Tokens → Create Token
- Copy the token immediately — it won’t be shown again
Connect provisioning (IdP side)
- In the Identity Provider tenant: Applications → Okta Org2Org → Provisioning → Configure API Integration
- Enter the SP Base URL and the API token, then click Test API Credentials
- Enable: Create Users, Update User Attributes, Deactivate Users
The API token you generate has the same permissions as the admin who created it. Use a service account rather than a personal admin token so provisioning doesn’t break if that person leaves.
Step 5 — Assign Users and Test
- In the IdP tenant: Applications → Okta Org2Org → Assignments → assign target users or groups
- Log in as an assigned user → click the Org2Org tile → confirm redirect to the SP tenant
- Check SP tenant → Directory → People to confirm the user was provisioned
- In SP tenant: assign the provisioned user to Dropbox Business
- Test the full flow: IdP login → Org2Org tile → SP dashboard → Dropbox tile → application access
- User authenticates successfully to Identity Provider
- Cross-tenant redirect works without errors
- User appears in SP Directory → People after first login
- Application assignment works for federated users
- End-to-end SSO completes without prompting for credentials again
Troubleshooting
Invalid SAML response
Issuer URI mismatch is the most common cause. The value in Okta SP must match the Issuer URI from the Org2Org app exactly — copy-paste, don’t type it.
API integration failing
Token permissions or wrong Base URL. Confirm the URL includes https:// and no trailing slash. Test credentials after every change.
User not accessing the app
Two assignments are required: the user must be assigned to Org2Org in the IdP and to the target application in the SP. Check both.
Key Points
- The Org2Org app in the IdP tenant and the SAML IdP in the SP tenant are two halves of the same connection — both must be configured before testing
- Use a dedicated service account to generate the API token so provisioning survives admin turnover
- JIT provisioning creates SP users on first login — if you need users pre-provisioned before they log in, trigger a manual push from the IdP tenant’s Org2Org Assignments tab
- Deactivation provisioning is critical — when a user is deactivated in the IdP, they should be deactivated in the SP automatically; verify this works before go-live
- The Org2Org developer account restriction is a common gotcha — if the IdP org is a free developer account, the Org2Org app won’t function